In this article, we’re covering an activity that’s terrorizing the ecommerce industry. It happens all over the world, it can happen to anybody, and it’s a multi-billion dollar industry. Everyone knows about it, but there’s not enough reliable information out there. To make matters worse, it’s a low-risk, high-reward activity for the people involved, making it very difficult to shut down.
You guessed it: today’s topic is carding.
According to statistics from 2018, card fraud is responsible for $24.26 billion lost globally. Credit card fraud increased by 18.4 percent in 2018, and it’s still going up.
Below, we’ll explain what carding is and point out some common signs. We’ll also share powerful techniques you can use to protect your customers’ credit card details, identify carding, and block common carding techniques.
What is carding?
Carding is a type of fraud where the perpetrator uses stolen card information to purchase prepaid gift cards which are then sold off. To accomplish this, fraudsters need to test whether a stolen credit card number can be used, so they visit ecommerce websites and initiate multiple transactions.
There are several types of carding:
- Multiple cards are repeatedly used in quick succession for low or identical dollar amounts.
- Multiple cards with the same name and/or billing address are used from the same IP address.
- A single card is repeatedly used in quick succession for low or identical dollar amounts.
- Multiple cards with different billing addresses but an identical BIN (Bank Identification Number) are used.
Here’s what a typical scenario in a carding attack could look like:
- A fraudster gets a list of stolen credit card numbers, either from a criminal marketplace or by compromising a website or payment channel. Their quality is often unknown.
- The fraudster sets up a bot to perform small purchases on multiple payment sites. Each attempt tests a card number against a merchant’s payment processes to identify valid credit card numbers.
- These bots attempt credit card validation thousands of times until they successfully identify valid credit card details.
- The validated card numbers are organized into a separate list and used for other criminal activity or sold to organized crime rings.
- Carding fraud often goes undetected by the cardholder until it’s too late.
Why ecommerce businesses should care about carding?
Ensuring that your customers have a pleasant, safe shopping experience with you should be a top priority as an ecommerce business owner. Shoppers want to deal with online businesses they can trust, which means that you have to put the right security measures in place to avoid carding attacks. Fraud triggers chargebacks, potential product loss, and irreparable damage to your reputation.
Running a business is tough enough— you certainly don’t need the avalanche of problems that come with data breaches or card fraud!
You need to know how to protect your store and your customers’ information. But first, let’s take a peek inside the popular carding websites and forums where these fraud ideas come to life.
Popular carding websites and forums
Carding websites and forums are illegal sites that are used to share stolen credit card data, carding methods, and results of carding attack exploits.
The main users in these forums are individuals who want to fraudulently purchase goods online and criminal groups in search of bulk credit card details that they can later sell on the dark web.
The organizers of carding websites and forums hide them using TOR browsers, and fraudsters make payments for stolen card details in cryptocurrency to avoid tracking by the authorities.
There have been vigilante attacks on these websites recently, including a major data breach of major carding forum, BriansClub. Known as one of the web’s largest marketplaces for stolen card data, BriansClub incurred an estimated loss of $4 billion in a 2019 data breach.
Ouch.
How do fraudsters carry out credit card fraud exactly?
Fraudsters have more than a few tricks up their sleeve for carding. However, there are some go-to carding methods used by criminals all over the world.
A phishing attack is the most common way fraudsters get credit card information. This method involves setting up malware and encouraging the target to download a malicious file. Once the malware is downloaded, hackers gain access to the target’s bank identification number, passwords, and other relevant details.
Hackers also carry out carding attacks through rootkit malware and unauthorized account takeovers. Rootkit malware is like an invisibility cloak for a malicious program. The malware protected by rootkit can survive multiple reboots and blends in with regular computer processes, letting hackers control your computer remotely and remain undetected.
Recently, a hacker group that goes by the name of EvaPiks attempted to compromise PCs at embassies for countries like Italy, Kenya, and the US by emailing Excel spreadsheets loaded with virus or malware on system that would then hijack a computer using the remote access app TeamViewer.
Investigations have linked this group to a hacking forum that discusses credit card theft, account takeovers, and similar topics.
Another popular technique criminals use for carding fraud is credit card skimming. Credit card skimming is a type of credit card theft where crooks use a small device to steal credit card information in an otherwise legitimate credit or debit card transaction.
When a credit or debit card is swiped through a skimmer, the device captures and stores all the details stored in the card’s magnetic stripe. The stripe contains the credit card number, expiration date, and the credit card holder’s full name. Thieves use the stolen data to make fraudulent charges either online or with a counterfeit credit card.
How to identify carding?
Prevention starts by recognizing the signs. If any of the following occur, there’s a good chance that carding or another type of fraud is happening on your ecommerce website:
- Low average shopping cart size
- A suspiciously high percentage of failed payment authorizations
- Extremely high shopping cart abandonment rates
- Disproportionate use of the payment step in the checkout process
- An increase in chargebacks
- Multiple failed payment authorizations from the same user, IP address, user agent, session, device ID or fingerprint
How can you avoid carding?
As an ecommerce store owner, there are some proven tips you can use to protect your store and your customers against this type of cybercrime.
1. CAPTCHA:
A CAPTCHA is a challenge-response test that helps an online merchant verify that a user is a human shopper. Yes, they can be very annoying to fill out sometimes, but they’re effective in preventing card cracking and other types of card fraud that occur via bots.
Traditional CAPTCHAs rely on static challenges, but reCaptcha elevates the bar with machine learning and dynamic tests like identifying objects in images or tackling intricate puzzles. So, how reCaptcha works? ReCaptcha works by using advanced challenges, like identifying objects in images or solving puzzles, to distinguish between human users and bots.
For example, your shoppers might be asked to read and type in distorted text, identify pictures that have a particular pattern, or answer a simple math question. These measures help protect your website from automated bots.
2. Address Verification System (AVS):
An AVS check compares the billing address used in the transaction with the issuing bank’s address information on file for that cardholder. Depending on whether they match fully, partially, or not at all, you can decide to accept or cancel the order.
Here’s how it would work: the cardholder provides their credit card’s billing address at checkout, and the AVS compares the address they entered with the one in the card issuer’s system to verify it. If the shopper fails this test, the transaction is automatically declined.
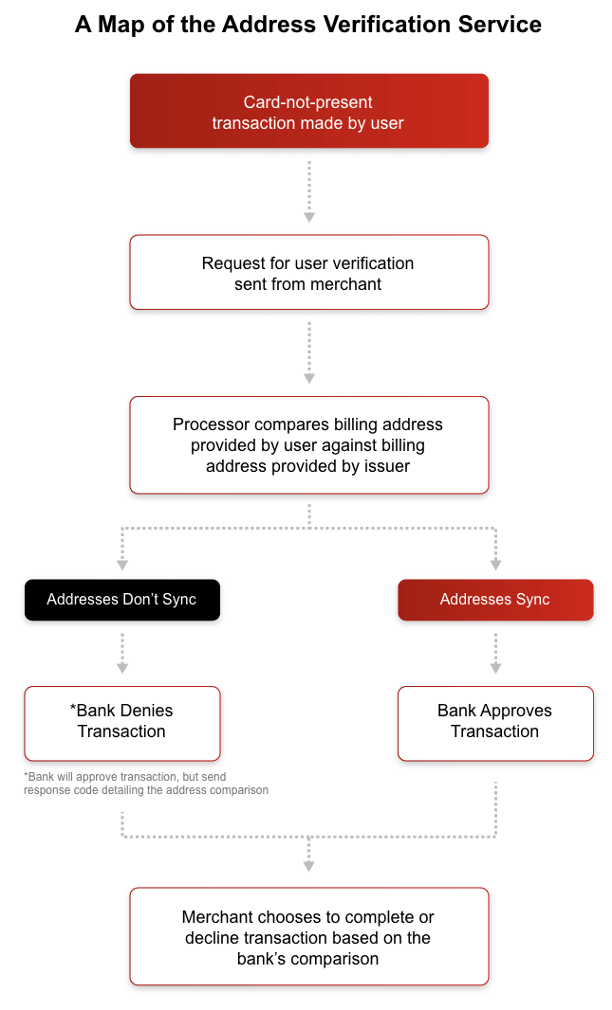
Source: Chargebacks911
3. IP Geolocation Checks:
Hackers from one part of the world can corrupt a computer in another part of the world while remaining anonymous. Fortunately, IP geolocation checks can confirm if the details of a purchase made from a certain country correspond to other known banking and invoicing records.
An IP geolocation check verifies information including latitude and longitude, time zone, region, city, country, postal code, Internet service provider (ISP), and more. These details offer more insights to help assess if incoming transactions are fraudulent or legitimate.
4. BIN Number Tracking:
A bank identification number (BIN) represents the first four to six digits on a credit card. These numbers identify the financial institution that issued the card. Besides identifying the financial institution, the BIN can track the geographic location of the bank branch that issued the card.
Merchants can detect possible cases of fraud and identity theft by comparing the geographic location of the cardholder to the location provided by the BIN. While fraudsters can use known BIN numbers to generate a card number, it’s impossible for them to guess the cardholder’s details. BIN number tracking can help identify potential red flags, like if the issuing bank address/country doesn’t match the shipping address or IP address, whether it’s a prepaid card, and more. You can use this information to improve your fraud prevention strategy.
5. Velocity Checks:
Velocity is the speed at which shoppers make transactions. Merchants can use this metric to identify irregular patterns in the checkout process that might point to fraud.
For example, it’s unusual for someone to make several purchases within seconds or minutes. As a merchant, you can choose to decline transactions if it appears that a robot is testing stolen credit card numbers in rapid succession.
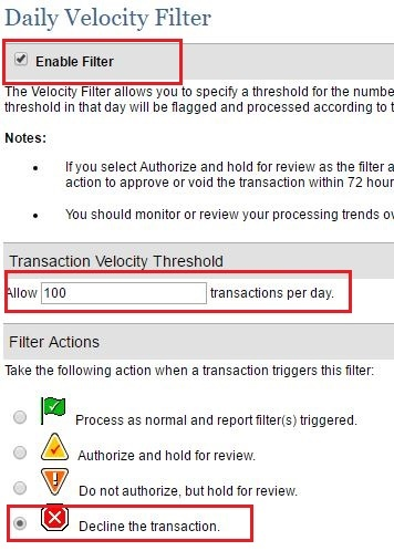
Source: Authorize.net
6. Authorization and capture
This is a 2-step transaction. Using this method, a merchant verifies that a shopper’s card can be charged, but holds off on collecting the funds from the card issuer.
By securing the funds, you can ensure you’ll be able to collect (or “capture”) them later, once you’ve verified that the transaction is not fraudulent.
If there are signs of fraud during the transaction review, you can cancel the transaction and avoid chargebacks.
Conclusion
In this article, we took a peek into the underground world of carding forums and websites where these sinister plans take shape. We talked about the great lengths that criminals go to in order to avoid detection, and covered the most common methods hackers use to commit credit card fraud.
Credit card fraud is a major concern for ecommerce business owners and shoppers alike. The good news is that there are effective security measures that you can follow to reduce the chances that your store gets targeted by the perpetrators of this insidious cybercrime.
As cybercrime strengthens, we can’t simply accept carding and online fraud as “the cost of business.” We’ve got to keep fighting and remove as much of it as possible from the ecommerce landscape. Hopefully, you’ve found the list of proven techniques to prevent carding helpful, and you’ll use them to improve the security of your ecommerce store!
What’s been your experience with carding or online fraud? What methods are you looking to put in place to better protect your business and customers? Let me know below!












